TRADECORE TECHNOLOGIES Financial IT Experts
TradeCore is a leading provider of software for Securities markets worldwide. TradeCore products range from multi-asset, multi-venue trading systems, Algo trading platform, data research platform, market data, and connectivity solutions, integration, and customized solutions.
TradeCore is planned to be with innovative solutions, new products, and new capabilities. We work hard every day to advance our technology to meet your needs and important for the future of the market. Every day we invent and implement something new.
Product ranges to serve trading technologies need for a financial institution, brokerage house with wide scope from prop desk to retail clients.
We are rapidly expanding as a reliable IT partner in the fast-growing trading market with a truly global approach and customer support backed up by an expanding network of representatives serving an internationally diversified client base with a comprehensive product set.
BLOG

Microsoft Azure vs AWS vs. Google Cloud
It presents a robust Infrastructure as a Service portfolio in addition to highly effective Platform as a Service features, especially for Windows purposes. Altogether, cloud services provide the unparalleled potential for enhancing business efficiency and rising earnings, and here we’ll have a look at one of the best cloud computing service providers. Like other cloud service providers, IBM cloud offers customers a plethora of merchandise to choose from. 49% of IT managers utilizing public cloud platforms, show an inclination in direction of Google Cloud Platform. Right from application and storage to computing providers, google cloud offers a plethora of functionalities.
Security and privacy breaches stand as two of the biggest roadblocks within the mass adoption of IBM Cloud. Additionally, users have reported a loss in the management of knowledge as one of the drawbacks of IBM Cloud when in comparison with other cloud service suppliers. A simple setup with reasonably priced pricing, DigitalOcean is one of the highest cloud service suppliers for the proper causes. By allowing builders to accomplish simple duties in a quick time, it’s turning into a preferred option for lots of techies, consolidating a revenue of $250 million. This tends to use the place clients are deploying across multiple vendors’ infrastructure and in addition, want to maintain some applications on-premise. Vendors have responded with a range of solutions to assist serve these clients who aren’t prepared to leap all-in on the public cloud simply yet, which is in fact the overwhelming majority of giant enterprises.
It requires customers to submit a ticket by way of the Azure portal and only subscription administration and billing support is included with the Azure subscription. Technical assist is simply provided if you purchase an Azure Support Plan which ranges from $29-$1,000 depending on the stage chosen, and tickets don’t get answered instantly. Along with poor help, Azure has had important outages similar to one in September of 2020 that lasted for 5 hours.
Cloud computing allows an enterprise to chop their operational and fixed month-to-month prices of hardware, databases, servers, software licenses. All hardware, database servers, internet servers, software program, merchandise, and companies are hosted in the cloud and added to an account as needed. Since AWS is the oldest cloud provider company, it has a lot more users and bigger neighborhood support. Companies like Netflix, Airbnb, Unilever, BMW, Samsung, MI, Zynga, and so forth are closely reliant on AWS Cloud services. These companies are considered as one of many greatest contributors to the AWS Global share market. Because cloud companies are run via software program platforms and virtualized networks, it signifies that it’s easy to access and analyze data for the needs of analytics in addition to for business intelligence purposes.
Oracle will put an optimized autonomous database in an enterprise and handle it as if it was its personal cloud. Microsoft CEO Satya Nadella argued that the company’s cloud unit sits in the middle of digital transformation efforts. AWS was the primary to offer cloud computing infrastructure as a service in 2008 and has by no means looked back.
Our preferred definition is provided by Gartner analyst Tom Bittman, who describes Private Cloud computing as being “defined by privateness, not location, possession or management responsibility”. In a Private Cloud setting, Virtual Machines function on a server, and any server resources not used by Virtual Machine A are utilized by Virtual Machine B, Virtual Machine C, and so forth. We are a professional evaluation website that receives compensation from the companies whose merchandise we evaluate. It additionally provides mobile apps for iOS and Android, permitting you to enter your information on the go.
Amazon Web Services and Google Cloud Platform provide complete steerage on their shared responsibility models for cloud safety. Take advantage of a cloud-based IAM service letting you add user sign-up, sign-in, and access control to your cellular and internet apps. This is the centralized IAM service giving you full visibility and management to handle your cloud resources. Giving directors the power to manage who can take motion on specific assets. Acting as the first line of defense on your IT infrastructure, a firewall is responsible for protecting your community from undesirable intrusion. Both Google Cloud and Amazon ship state-of-the-art firewall safety of their cloud platforms.
Google Cloud has a big selection of tools to ensure constant efficiency and management. These embody Compute Engine, App Engine, Container Engine, Cloud Storage, and Big Query. Google also offers clean migration to digital machines with versatile pricing. Google Cloud permits customers to create enterprise solutions using Google-provided, modular net companies.
Lastly, it was built with “customer-friendly pricing”, which aims to be less complicated and more understandable, and also decrease, than comparable cloud services. Google Cloud Platform, the most recent cloud-native competitor in the market, was launched in 2011 to offer a Cloud infrastructure to the preferred search engine “Google”. In less than a decade, GCP has proven its influence on the cloud industry, and under the legacy of Mr. Sundar Pichai, this platform has promised to bring about revolutionary domination available in the market. Cloud Computing has impacted the “Line of Technology” since its inception and now the customers are dealing with the dilemma of which Cloud Service Provider to go for and why? The battle for dominance has led to the revolutionary progress of the three most famous and dependable Cloud Service Providers — Amazon Web Services, Google Cloud Platform, and Microsoft Azure.
Many Companies Using Cloud Computing, SaaS From a SaaS Provider perspective
A recent article from Computerworld stated many companies are moving away from expensive enterprise IT infrastructure and toward “cloud-based” solutions. As a SaaS provider, I have to admit that I too am driven by the opportunities that cloud-based infrastructure presents us. We are seeing companies move away from expensive hardware and toward amazon cloud services, and the benefits can be extraordinary. However, we also see opportunities that cloud-based solutions can provide for the SMB community, and I’d like to explore those opportunities briefly.
1. Reduced Costs and Impact on People
When companies undertake massive investments in IT infrastructure and processing resources, it is easy to see how the impact can be felt immediately. However, these investments often have a very negative impact on the people responsible for using the existing infrastructure. Although it is often easier to put a dollar figure onto the impact of IT infrastructure costs, I’d like to explore another metric. The typical response or reaction from a manager when making a change in their infrastructure is “but I only have 80 people using it so I don’t really need 80 engineers to manage it”. Many times this statement is used may not be an accurate measurement of the impact of the change, and more often than not the impact is felt in very subtle ways.
How many of your people have heard the phrase “changing the infrastructure” and how many have felt the impact of that change? The impact is there. Understanding the symptoms of the change is the first step in preventing the change from occurring. Many change management techniques focus on the infrastructure, but it is important to look at the people who are actually using the infrastructure. A change can be implemented successfully by the department whose people make the change. You need to understand what people are doing and what their expectations are.
Why is there a need to understand the expectations of the change?
IT departments are trying to meet the business expectations. By understanding the impact that the change is having on your department, you will be in a better position to make any adjustments that are required.
Usually, the change is going to require new tools and new ways of doing things, and IT departments are not immune to this. If you have a nickel for every time you have to spend a couple of extra minutes animating a couple of extra tabs in your accounting system, you are going to feel the impact of the change in time.
When it comes to SaaS, the effect of the change may be negligible for the person using the legacy system, but for the department where that legacy system is based, it may be a major issue.
Wavelengths
There are 3 different wavelength strategies that cloud computing supports. They are:
- Ultrasonic hardwire
- Optical fiber (including SONET)
- McKinsey gauge
- Infrared hardwire
The first one is ultrasonic hardwire, used for voice and data applications in the regime of mater-to-mom cable, where cables are just made for data communications. This is old technology, and it tends to be costlier than its optical alternatives.
Optical fiber (including SONET)
This is the sequencing strand and is used for basic cloth cable. Optical fibers are made from glass or plastic, and they carry data across them very well. This is a good idea because few things are impervious to fiber optics.
Infrared hardwire
This is like playing with a bunch of fire loggers. It uses certain wavelengths of infrared, which are longer than the wavelengths of the visible light spectrum. Because of this, it is less susceptible to interference from unrelated sources, and it keeps the signal traveling farther before it loses strength.
Wi-Fi
This fourth option is wireless fidelity. It uses Bluetooth technology. This is a widely used wireless networking protocol and it is superior to the other two. Wi-Fi lets you share information with your network, which is a good thing when you have a small network of stations.
The positives of Wi-Fi
It’s easy to install. It’s quick. It’s very inexpensive. You can do it anywhere in the world where there is Wi-Fi. Some use their cell phones to do this.
Its advantages are very obvious. If you have a small network, use Wi-Fi. It’s very fast. It’s also very convenient. If you have a notebook, use Wi-Fi to download updates. Your things can be kept in the pocket of your pants. This is very helpful.
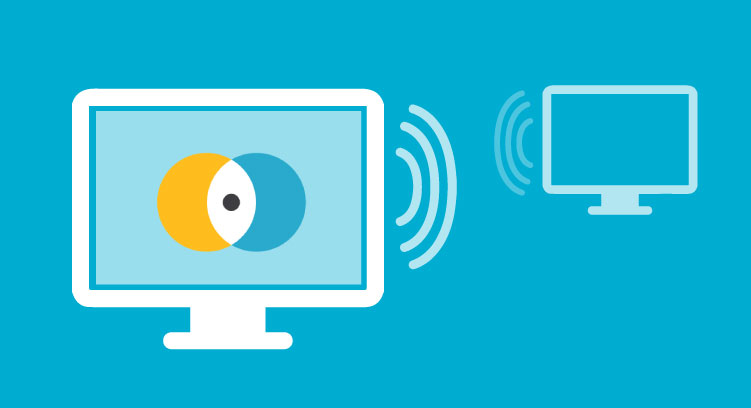
Remote Desktop Service
A remote desktop service is a protocol for giving access to a remote computer system by using a computer system or a device like a server with a login name and password. With the process, the user can access a computer system remotely and use it to access another machine or server that is connected to the same network.
Basically, the remote desktop is enabled when the user owns the computer system or the client is configured on the remote computer system. Later the user can log in to the remote computer system to use it. The remote desktop services can be used to access a machine even when the user is not connected to the local network.
Remote Desktop Services architecture is the basic infrastructure for offering the remote support solution to the client. The OSI model is used for defining the data link layer, data transfer layer, network layer, services layer, and remote procedures layer.
Using the OSI model, the Desktop layer is the lowest layer dedicated to the remote computer system. The computer that is owned by the client is connected to the remote computer system through the network and the user can log in to the computer system. The ownership model is beneficial because it ensures that the computer systems that are remote are authenticated. The users can gain access to the information that they want using the remote desktop service.
The Data Link layer offers the means through which the client can connect to the server. It can be a broadband connection through a secure router or through a Virtual Private Network (VPN) through either the LAN or through the Internet. The VPN services allow a remote user to access the private network from a remote location, allowing the remote user to work as if he is sitting at his desk. The Data Link layer offers the lowest level of service.
The Network layer helps the client to share the files, folders, and data between the computer and the server. The exact location of the data cannot be determined by the computer because it is copied to the server. The location of the data can be approximate.
On the other hand, the services layer allows the clients to extend the services that they have to the server, which extends the server jobs and capabilities. The server can be configured to provide the particular services that the client wants or even to simply not provide services at all if the client does not express the services that he needs.
The Remote procedure layer marks the place where the data of the remote computer can be stored, for example, in a file server. The desktop client browses through menus and the control panel remote procedure layer (DCL) is connected to the server.
The Desktop layer is the first level in the remote procedure layer. The components located in the layers below this are the server, the browser, the mail client, the news client, the fun client, the hardware, and the services.
In the desktop interface, the user can only display the properties of the remote computer. The DCL programs such as the desktop environment program and the remote procedure programs are loaded by the DCL automatically. All the devices that are connected to the computer during the desktop interface have to be configured in order to allow the computer to send and obtain data from them.
The remote procedure programs can be found by using the procedures keyword in the DCL. Two interfaces are used for the configuration of the remote PC. The keyword and the command line. When the router is connected to the remote PC, the router can be configured into the DCL or the trusted zone (the addresses range from 192.168.1.0/24 to 192.168.1.255/30). The advantage of this is that no PC is needed and everything is configured by the manufacturer.
The DCL interface’s creativeness switches off and on. They are basically flat wires with an on and off. The purpose is to send the commands to the router or the server. The routers and the servers have hosts names. These hosts can be changed at any time. What is remarkable about this is that these devices (known as PCs) can be found to the right of the router. All that is needed is a username and a password. These are known as SSID.
There are 3 different methods that can be used to change the setting of the username and the password. Firstly, the username can be changed directly without a password. Secondly, the password can be changed independently from the computer. That is, Changing the password does not require associating it with the router configuration. Changing the username is done in the background so it is not too visible.





The Best Small Investments Your Company Can Make
If you want to run a successful company, you are going to need to invest some time in money into it. Obviously, there are plenty of investments you can make, such as buying another building to open another store or investing in a new kitchen if you own a restaurant. However, not all investments need to cost hundreds of thousands of dollars and take years to finish. Some upgrades and investments are relatively inexpensive but still create a positive return on investment. Here are a few of the best investments you can make.
Upgrades
You can invest in upgrades for your computer, your network, your office equipment, and even your storage systems. The technology for these upgrades is available among various hardware brands, and you can choose between buying new equipment and updating your current equipment. By choosing the latter, you will save money because you did not purchase the outdated equipment and you will be able to continue with your current operations.
Investments
You can also make money from investments. In the computer industry, for example, new software and anti-virus programs represent good investments. Software is particularly expensive, and you can usually spend an entire day exploring the online market for the best deal.
For office equipment, you can invest in longer-lasting office equipment and desks. Investing in durable computer desks is a great way to protect against belongings disposal, damage, accidents, and mold growth – all of which cost your company money.
Malfunctions
Technology malfunctions are defined as events that interfere with the normal use of a product, application, or service. From hardware failures to software compatibility issues, these events often require time-consuming IT support that your employees cannot handle on their own. For this reason, you should always invest in technology and computer monitoring services that employ qualified technical experts.
During difficult economic times, implementing budget cuts on your employees’ time can create a needless challenge to your business. Employees will be tempted to waste time looking for work and not performing their job correctly. Neglect these challenges by investing in the right technological support.
Friendly Like-Minded Technology Support
From computer crashes to system failures, from viruses to data recovery, and from human error to environmental hazards, there are many reasons that can mean a deferment or loss of productivity. For example, if your computers are running undetected viruses, it may mean that your computers are infected and the source of the virus is not yet known. If your computers have encountered a replicate adware infection, it may also mean that the source of the virus is not known.
A computer virus is a malicious piece of code that most likely came off a malicious disk and was designed to interfere with the operation of your PC or to command your computer to do something it was not programmed to.
When it comes to computer systems, there are two types of threats – known and unknown. When you first get your PC set up, it runs well. But as time goes by, you may start to notice that things are changing, things are running slower than usual, and you are starting to get dreaded computer ‘crashes’…
No matter what the source of the problem is, you can reduce its impact on your work. First and foremost, you should keep your computer anti-virus up-to-date. Virus protection has gotten much more advanced – it’s much easier to delete an infected PC than it is to kill an entirely good used computer. So, don’t wait. If your computer is running slow, act quickly to download and install updates for your antivirus software.
Anti-Spyware Programs
Anti-Spyware programs are great tools that aid in monitoring your background and overall behavior on the internet. It does so by acting as an anti-spyware counterpart to your internet browser. Your browser becomes aware of each time you enter a website and instead of retrieving the website from memory, it sends the site to your computer for faster viewing. Anti-Spyware software adds a number of other functions and aspects that make it beneficial to your computer.
System Monitoring
Your system monitoring software should always be running and you should be able to reach it anytime you want to. However, it is important to realize that while it is possible to keep your software updated all the time, it can also be useful to shut down your computer occasionally and let your computer check something before opening it again.
Memory Patching
Needless to say, adding memory can make your computer run faster. It is easy to do, so anyone can do it. However, you can only do it regularly, and as a hobbyist, you may not be able to reach your full potential. You may be able to patch your computer up to the point where you can turn it off completely, but how well you’d improve your computer’s performance will depend on the nature of your work.